A sophisticated iPhone hacking toolkit originally developed with US government funding has leaked to criminal groups who are now using it against ordinary users, according to new research from Google and mobile security firm iVerify.
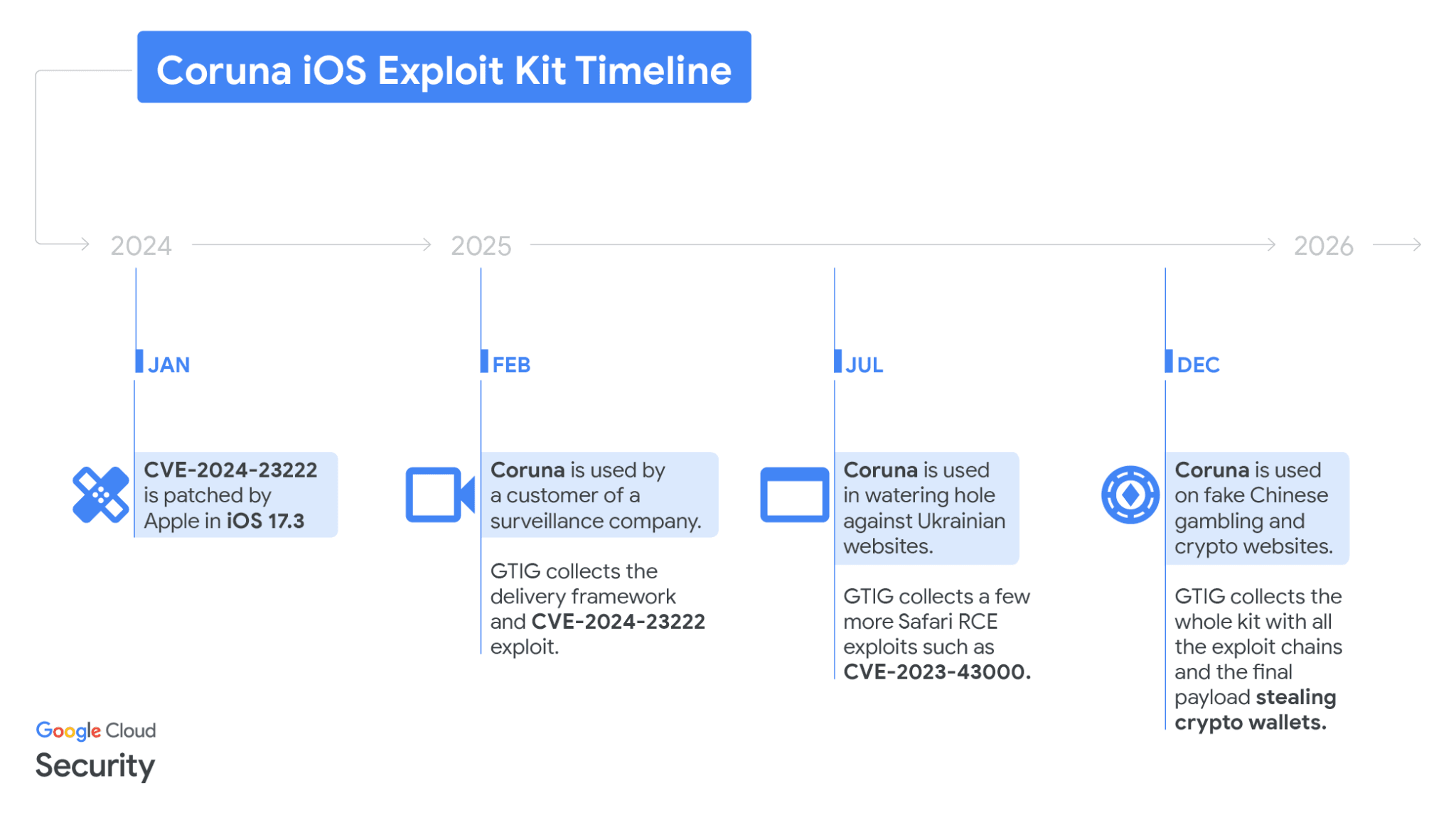
The "Coruna" exploit kit combines five full attack chains and 23 vulnerabilities to compromise iPhones running iOS versions 13 through 17.2.1, Google's Threat Intelligence Group revealed. Devices updated to iOS 26 are protected, but approximately one-quarter of compatible iPhones remain vulnerable.
Attackers deliver Coruna through compromised websites using hidden JavaScript that checks device models and iOS versions before launching multi-stage exploits. The toolkit bypasses Apple's built-in protections, escalates system privileges, and installs malware capable of harvesting sensitive data or downloading additional components.
Reverse engineering by iVerify indicates Coruna shares technical foundations with known US government hacking tools.
"It's highly sophisticated, took millions of dollars to develop, and it bears the hallmarks of other modules that have been publicly attributed to the US government,"
said iVerify cofounder Rocky Cole in a statement published by AppleInsider.
The toolkit appears to have leaked from government control and is now deployed by Russian intelligence actors and China-based cybercriminal groups in what researchers describe as "the first observed mass exploitation of mobile phones by a criminal group using tools likely built by a nation-state."
Coruna spreads primarily through "watering hole" attacks on fake cryptocurrency services designed to lure victims to malicious pages. Once installed, the malware focuses on extracting digital wallet data and recovery phrases, revealing clear financial motives behind current operations.
Security researchers found around 42,000 devices may already have been compromised with a specific version of Coruna used in Chinese-language cybersecurity attacks. A separate Russian espionage operation also used the tool against an unknown number of Ukrainians.
The exploit kit includes built-in safeguards that prevent attacks under certain conditions. Coruna checks whether Apple's Lockdown Mode is enabled and immediately terminates if detected.
It also fails when users browse in private mode and cannot impact devices running the latest iOS versions.
Apple specifically rendered Coruna ineffective with iOS 26 updates earlier this year. Approximately 74% of iPhones capable of running iOS 26 had updated to the operating system as of February 12, leaving a portion of older devices exposed.
"This is the first example we've seen of very likely US government tools spinning out of control and being used by both our adversaries and cybercriminal groups,"
Cole added in his statement about the toolkit's unexpected proliferation.