Traveling exposes your smartphone to unique security risks. From airport security checkpoints to public Wi-Fi networks, your personal data faces threats you might not encounter at home. With a few simple precautions, you can significantly improve your phone's protection while on the road.Update Your Software Before You Go
Before traveling, ensure your smartphone's operating system and apps are fully updated. Software updates often include critical security patches that fix vulnerabilities hackers could exploit. These patches address known security gaps that cybercriminals actively target.
Use Strong Authentication Methods
Set up strong password protection or biometric authentication like fingerprint or facial recognition to lock your phone. Avoid simple patterns or easily guessable passwords. A combination of letters, numbers, and symbols provides the best protection against unauthorized access.

Enable Two-Factor Authentication
Activate two-factor authentication (2FA) for your important accounts. This adds an extra layer of security by requiring a second form of verification, such as a code sent to your phone, in addition to your password.
Be Smart About Public Wi-Fi
Public Wi-Fi networks are prime targets for hackers. Avoid accessing sensitive information like banking apps or entering passwords over public networks. If you must use public Wi-Fi, a Virtual Private Network (VPN) encrypts your internet connection and protects your data from interception.
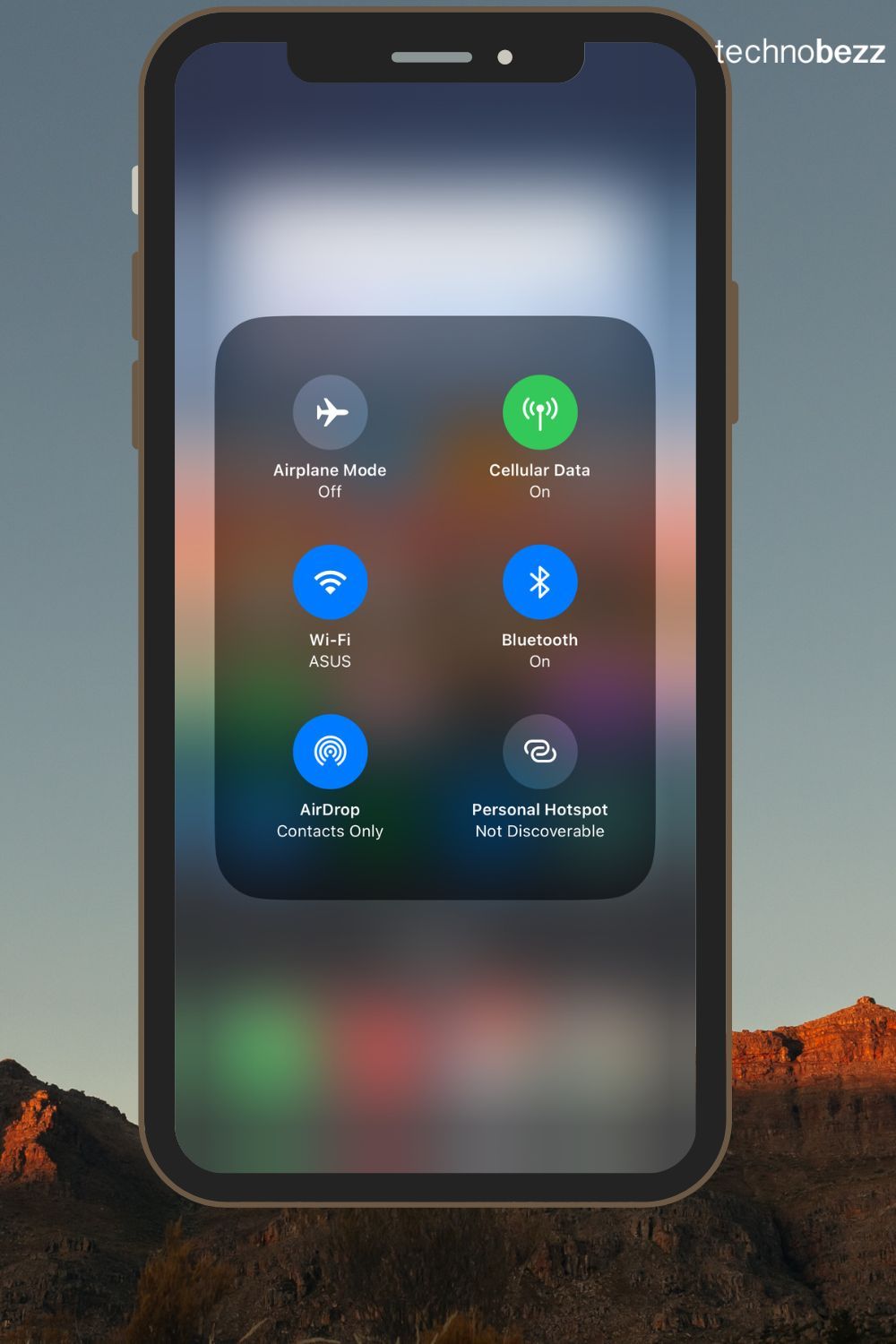
Turn Off Automatic Connections
Disable automatic Wi-Fi connection features on your phone. This prevents your device from connecting to unknown or potentially malicious networks without your permission. Manually select trusted networks rather than letting your phone connect automatically.
Use a VPN for Secure Browsing
A VPN encrypts your internet traffic, making it much harder for hackers to intercept your data. Choose a reputable VPN service and use it whenever you connect to the internet, especially on public networks. This creates a secure tunnel for your online activities.
Watch for Phishing Attempts
While traveling, you might receive emails or messages from unfamiliar sources. Be cautious about clicking links or downloading attachments from unknown senders. These could be phishing attempts designed to steal your personal information or install malware on your device.
Read more - What to Do When You Receive a Phishing Email (and How to Protect Yourself)
Install Security Apps
Consider installing security apps that offer features like anti-virus protection, malware scanning, and theft prevention. These apps can provide an additional layer of security and alert you to potential threats.
Manage Bluetooth Connections
Turn off Bluetooth when you're not using it. Bluetooth can be another entry point for hackers seeking unauthorized access to your phone. Only enable Bluetooth when actively pairing with trusted devices.
Keep Your Phone Physically Secure
Physical security is just as important as digital protection. Keep your phone close to you in crowded places to prevent theft. Use secure pockets or bags, and be mindful of your surroundings, especially in tourist areas.
Backup Your Data Regularly
Regularly back up your phone's data to a secure cloud service or external storage. This ensures you can recover your information if your phone is lost, stolen, or compromised during your travels.
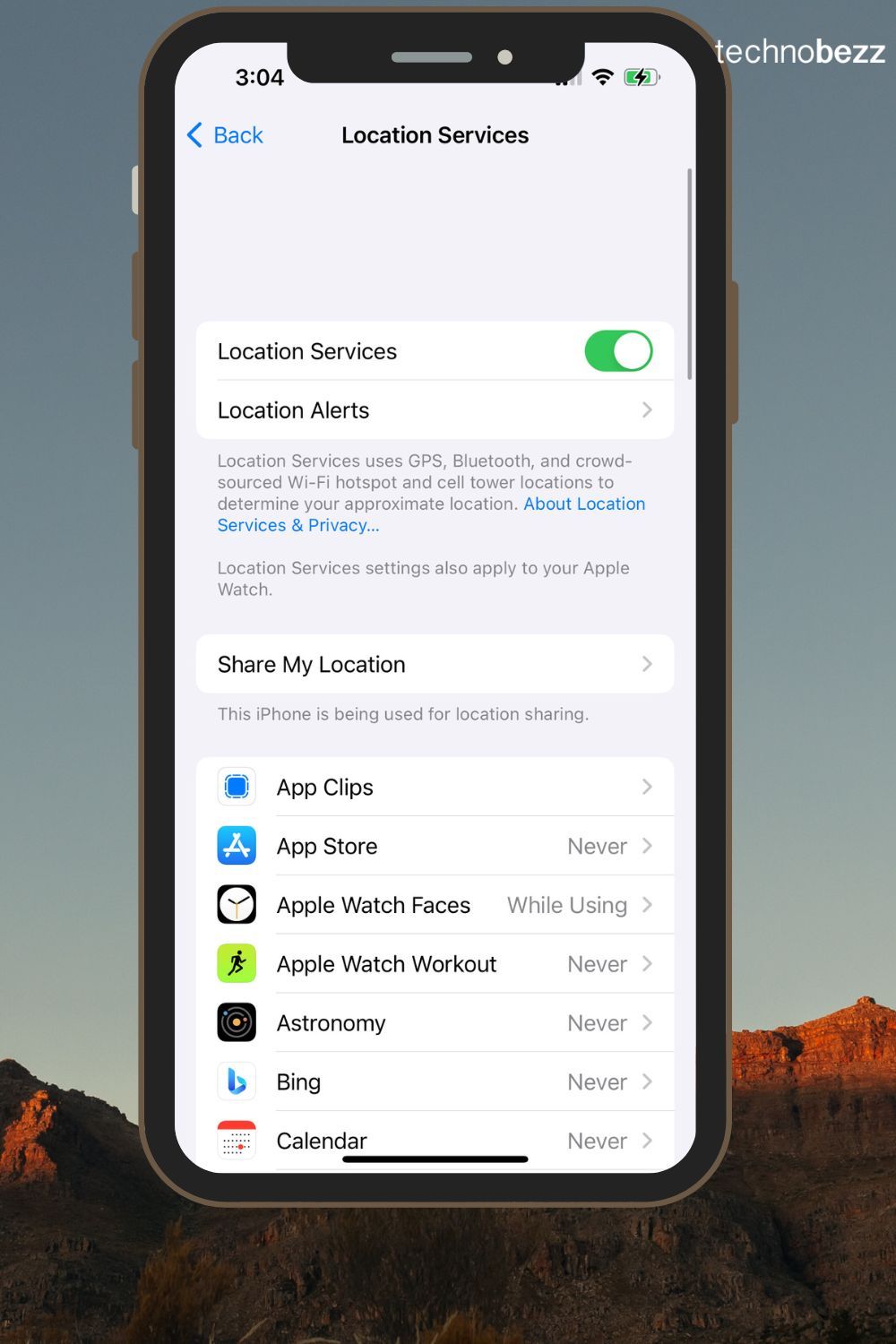
Disable Unnecessary Services
Turn off services you don't need while traveling, such as location services, mobile data, and NFC when not in use. This reduces the number of potential entry points hackers can exploit and conserves battery life.
Use Encrypted Communication Apps
Choose apps that offer end-to-end encryption for your communications. Encrypted messaging apps ensure that only you and the intended recipient can read your messages, protecting your conversations from interception.

Monitor Your Accounts
Regularly check your bank and email accounts for any suspicious activity while traveling. If you notice anything unusual, take immediate action by changing passwords or contacting your financial institutions.
Set Up Remote Wipe
Enable remote wipe features on your phone. If your device is lost or stolen, you can remotely erase all data to prevent it from falling into the wrong hands. Both Apple and Android devices offer this security feature.
Limit Virtual Access Points
Download necessary software before traveling and disable Bluetooth and Wi-Fi when not actively using them. Avoid sharing your location with apps unless absolutely necessary to minimize your digital footprint.
Use Outlets Instead of USB Ports
Avoid using public USB charging stations, which can be tampered with to steal your data through a technique called "juice jacking." Use regular electrical outlets or a personal power bank instead to charge your devices safely.
Why Public USB Ports Are Risky
- Juice Jacking: Hackers can install malware or steal data through compromised USB charging ports
- Fake Charging Stations: Some criminals set up fake charging stations designed specifically to steal information from connected devices
- Data Interception: Public USB ports can be modified to intercept data transfers between your phone and the charging source

Power Down Devices Frequently
When traveling, power down your devices regularly, especially at security checkpoints. Devices are more secure when completely shut down, as many forms of malware and remote access tools cannot operate when the device is off. This also prevents potential data interception at border controls and reduces tracking through rogue networks.